IT security has become more accessible than ever with the arrival of public clouds. Many common security services have been made available to the common man from the click of a button and all within the same platform. You would think that by now, IT environments hosted in Amazon Web Services (AWS), Azure or Google Cloud Platform (GCP) are more secure than ever – at least compared to on-premise. Unfortunately, this is not the case.
The rise of the public cloud is explained by its ease of adoption and rapid deployment. Organization can finally focus on what they are good at: doing business and innovate using solutions that provide business advantage. Cloud assets can be spun-up and torn-down on demand. Cloud accounts can be opened with few clicks and new services can be activated within minutes.
Traditional enterprise security controls lack agility and flexibility.
This is also the very thing that makes cloud environments so challenging to secure. It is the loss of control and visibility that lead to new security risks. Traditional enterprise security controls lack agility and flexibility, and due to this security teams are often left in the dark on what is going on with cloud deployments. The result: security weaknesses, such as rogue assets, forgotten assets and misconfigured or forgotten user accounts abound.
Misconfiguration happen more often than you would think. In fact, it is the norm, not the exception. According to Gartner, nearly all successful attacks on cloud services are the result of customer misconfiguration, mismanagement, and mistakes. So, how to tackle these misconfigurations?
So, how to tackle these misconfigurations?
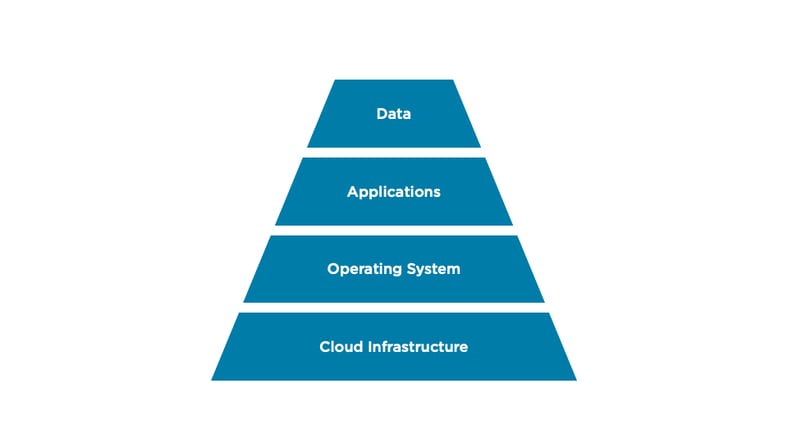
The basic foundation of securing a cloud environment and taking back control over misconfigurations is gaining full-stack visibility into all its assets. Cloud security is impossible without full-stack visibility – you cannot protect what you cannot see. Full-stack visibility means complete understanding of what is happening in the entire cloud environment, across all of its layers:
Luckily, cloud providers offer cloud-native services and solutions to help with this. But as you can guess, this is easier said than done. Many organizations lack the knowledge and governance to do this right. Not to mention that you would need to overlay multiple tools provided by the cloud provider as these often only solve one piece of the puzzle. This patchwork is operationally cumbersome and does not provide the complete coverage of assets.
Common methods to help with overall visibility into the cloud include agent-based solutions, network scanners, and cloud security posture solutions (CSPMs). Unfortunately, in our opinion, none of these are capable of protecting cloud assets across all the four layers.
Overlaying multiple tools is operationally cumbersome.
There is, however, a new generation cloud asset visibility solution that delivers in-depth, full stack visibility – called Orca Security. We are excited to announce that we have partnered with Orca Security to help our customers achieve full-stack visibility across their cloud environments, such as AWS, Azure and GCP.
Delivered as a SaaS solution, Orca Security uses its patent-pending SideScanning™ technology to deliver instant and agentless deeper visibility into your cloud environment and ease compliance efforts. The solution works out-of-band and scans the entire cloud estate, down to the data layer to identify malware, vulnerabilities, misconfigurations, leaked passwords, sensitive data (PII) and more.

Free trial with our HealthCheck
Each CloudNation HealthCheck comes with a free trial1 of Orca Security to give you the opportunity to experience full-stack visibility yourself. The CloudNation HealthCheck is a security assessment we have developed to help you identify misconfigurations and other security risks within your cloud environment. It is quick and comes with actionable recommendations to help you start fixing right away.
Interested? For more information on Orca Security or our HealthCheck, please leave your contact information below or gives us a call.
Contact us
1Terms and conditions may apply





